Guard yourself from tracking, surveillance, and censorship.
The Tor Browser harnesses the power of the Tor network to safeguard your privacy and anonymity. Utilizing the Tor network offers two primary benefits:
Moreover, Tor Browser is engineered to thwart website fingerprinting techniques aimed at identifying you based on your browser setup.
By default, Tor Browser doesn’t retain any browsing history. Cookies are only effective for a single session (until Tor Browser is closed or a New Identity is requested).
With the next generation of internet exchanges focused on maximum privacy and security, a variety of ways have been enforced to maintain them as such. Censorship has been shifted from the streets to the digital domain, forcing the standard citizen to derive alternative ways to maintain anonymity. A major weapon in this battle for privacy and security is the Tor Browser, an independent browser meant to browse the internet while relaying information through the Tor network. It serves as a meaningful alternative to the standard internet browsing habits. Let’s delve deeper into the workings of the Tor Browser.
Tor constitutes a network of virtual tunnels engineered to enhance your privacy and security while traversing the Internet. Its operation involves routing your traffic through three randomly selected servers, commonly referred to as relays, within the Tor network. Subsequently, the final relay in this circuit, known as the “exit relay,” forwards the traffic onto the public Internet.
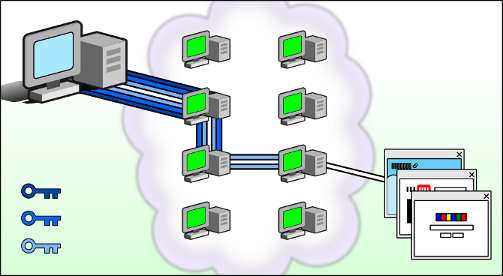
The depicted image showcases a user engaging in browsing various websites via Tor. The green intermediate computers symbolize relays within the Tor network, while the three keys symbolize the layers of encryption safeguarding the connection between the user and each relay.
The Tor Network, short for the Onion Router, is an open-source privacy network that permits users to browse the web anonymously. Initially developed and solely used by the U.S. Navy to protect sensitive government communications, the Tor Network intercepts traffic from a user’s browser and bounces their request off a random number of other user IP addresses. These IP addresses belong to volunteer devices known as nodes or relays. By encrypting the traffic and moving it across different Tor relays within the network, the Tor Network disguises user identities and makes tracking difficult for both ISPs and malicious attackers.
The Tor Browser, developed by a non-profit organization as part of the Tor Project in 2008, is a browser forked from the popular Firefox that anonymizes web traffic using the Tor Network. It simplifies the process of maintaining anonymity over the internet, which previously demanded a lot of knowledge and practice from users. The Tor Browser’s major features include the ability to delete all browser history, cookies, and tracking data the moment it is closed, thereby preventing usage habits from being tracked and singled out.
The highlight of using the Tor Browser is to maintain anonymity over the internet. By routing information through multiple nodes and relay servers, the Tor Network obfuscates user IP addresses from unwanted surveillance, making it entirely difficult for ISPs to keep track of usage data. Additionally, Tor Browser offers access to onion links, which are only available within the Tor Network and provide services like online shopping and cryptocurrency transactions without the risk of spying by authorities.
Many people believe that a VPN offers the same benefits as the Tor Browser. However, there are significant differences between the two. Tor is completely free and open-source, allowing the code for the browser and the network to be audited for security concerns. Furthermore, Tor handles multiple layers of encryption and routes data through multiple servers, making it slower compared to VPNs. Additionally, the nodes and relays used in the Tor Network are volunteer, providing straightforward jurisdiction.
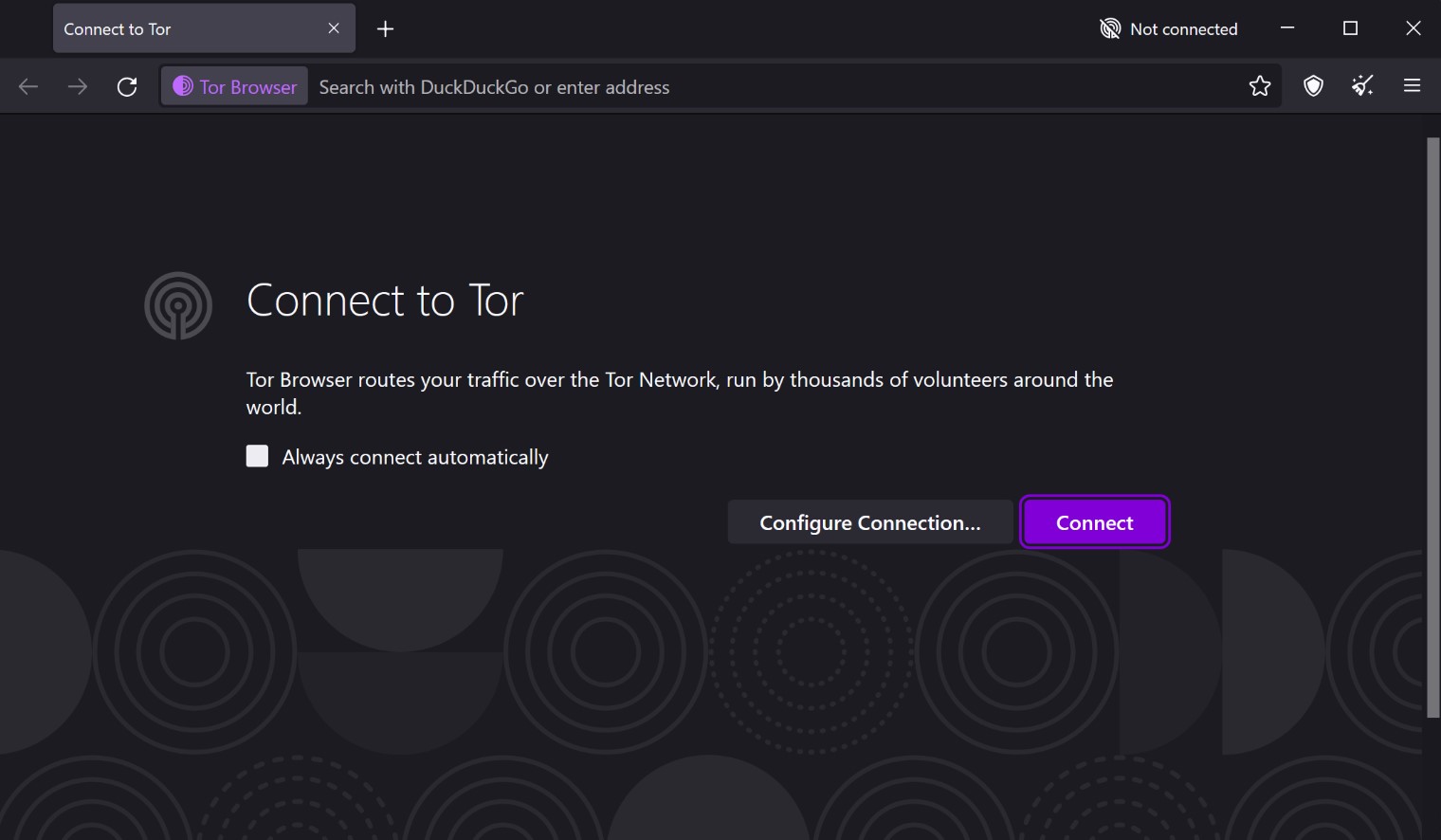
On opening the Tor Browser for the first time, users are welcomed with a page that allows them to connect to the Tor Network. The Tor Browser anonymizes and protects internet usage by routing traffic through multiple nodes and relay servers, making tracking difficult. Additionally, it provides access to onion links, which are only available within the Tor Network, offering users privacy and anonymity while browsing the internet. In conclusion, the Tor Browser stands as a powerful tool for maintaining anonymity and privacy over the internet. With its robust network infrastructure and emphasis on user privacy, it continues to be embraced by journalists, dissidents, and privacy-conscious individuals worldwide. Embracing technologies like the Tor Browser is crucial in safeguarding digital privacy and promoting freedom of expression in the digital age.
Visit the Tor Project Website: Type “tor project org” into your browser’s address bar and navigate to the official Tor Project website.
Download Tor Browser: Click on the “Download Tor Browser” button located at the top right corner of the website. Choose the appropriate version for your operating system (Windows, Mac, Linux) and start the download.
Install Tor Browser: Once the download is complete, open the downloaded file and follow the installation instructions. On macOS, drag the Tor Browser icon into your Applications folder.
In regions where Tor faces blocking, users can configure Tor to connect via a bridge during the setup phase. However, if Tor isn’t connecting and censorship isn’t the issue, one of the primary culprits might be an inaccurate system clock. Ensure that your system clock is correctly set to resolve this issue.
It’s important not to use Tor for torrenting. Tor Browser intentionally blocks browser plugins like Flash, RealPlayer, and QuickTime because they can be manipulated to expose your IP address. We strongly advise against installing extra add-ons or plugins in Tor Browser as they might bypass Tor or compromise your privacy. Tor Browser is already equipped with features like HTTPS-Only mode and NoScript, along with other patches to enhance your privacy and security.